I have developed a fast emulator for modern shellcodes, that perform huge loops of millions of instructions emulated for resolving API or for other stuff.
The emulator is in Rust and all the few dependencies as well, so the rust safety is good for emulating malware.
There are shellcodes that can be emulated from the beginning to the end, but when this is not possible the tool has many features that can be used like a console, a memory tracing, register tracing, and so on.
https://github.com/sha0coder/scemu
In less than two seconds we have emulated 7 millions of instructions arriving to the recv.
At this point we have some IOC like the ip:port where it's connecting and other details.
Lets see what happens after the recv() spawning a console at position: 7,012,204
target/release/scemu -f shellcodes/shikata.bin -vv -c 7012204
The "ret" instruction is going to jump to the buffer read with recv() so is a kind of stager.
The option "-e" or "--endpoint" is not ready for now, but it will allow to proxy the calls to get the next stage automatically, but for now we have the details to get the stage.
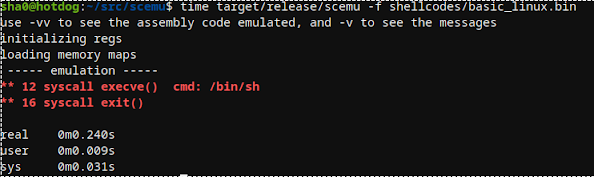
SCEMU also identify all the Linux syscalls for 32bits shellcodes:
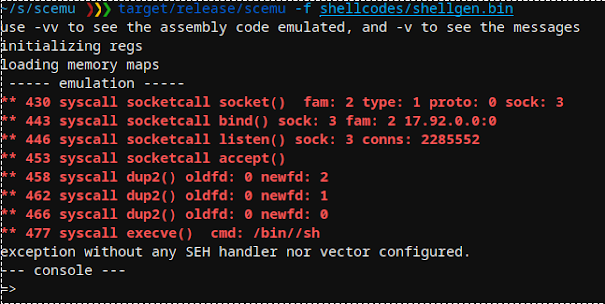
The encoder used in shellgen is also supported https://github.com/MarioVilas/shellgen
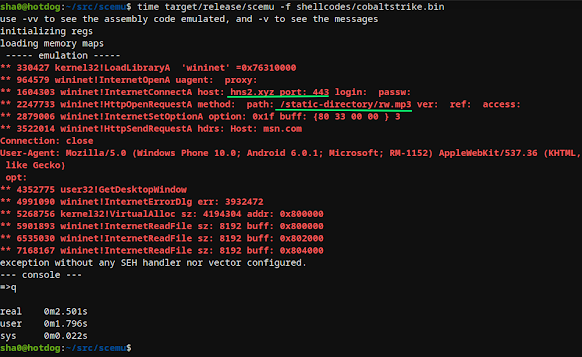
Let's check with cobalt-strike:
In verbose mode we could do several greps to see the calls and correlate with ghidra/ida/radare or for example grep the branches to study the emulation flow.
target/release/scemu -f shellcodes/rshell_sgn.bin -vv | grep j
target/release/scemu -f shellcodes/rshell_sgn.bin -vv -c 44000 -l
More articles
- Hacking Tools Download
- Pentest Tools Open Source
- Hacking Tools Online
- Game Hacking
- Hack Apps
- Hacker Tools For Mac
- Pentest Tools Open Source
- Pentest Tools Alternative
- Pentest Tools Linux
- Hacker Tools 2019
- What Are Hacking Tools
- Github Hacking Tools
- Hack Tools For Ubuntu
- Top Pentest Tools
- Pentest Tools Framework
- How To Make Hacking Tools
- Bluetooth Hacking Tools Kali
- Hack Tools Pc
- Hacking Tools Usb
- Hacking Tools Usb
- What Are Hacking Tools
- Pentest Tools Nmap
- Pentest Tools For Ubuntu
- Termux Hacking Tools 2019
- Best Hacking Tools 2020
- Pentest Tools Android
- Pentest Tools List
- Hacker Tools Free
- Best Pentesting Tools 2018
- Hacker Tools Free Download
- Hacking Tools Online
- Tools Used For Hacking
- Nsa Hack Tools
- Hack Tools
- Hacker Tools
- Hacking Tools For Windows 7
- Pentest Tools Tcp Port Scanner
- Pentest Tools Online
- Hack Tools
- Pentest Tools Find Subdomains
- Tools Used For Hacking
- Pentest Tools Tcp Port Scanner
- Pentest Tools Android
- Hack Tools Online
- Pentest Tools Bluekeep
- World No 1 Hacker Software
- Pentest Reporting Tools
- Pentest Recon Tools
- Hacker
- Hacker Tools For Mac
- Hacking Tools Free Download
- Hacker Tools For Windows
- Underground Hacker Sites
- Hacker Tools For Windows
- Black Hat Hacker Tools
- Hacking Tools Usb
- Nsa Hacker Tools
- Hacking Apps
- New Hacker Tools
- Hacking Tools Free Download
- Best Pentesting Tools 2018
- Nsa Hack Tools
- Pentest Tools Android
- Computer Hacker
- Hacking Tools For Kali Linux
- Pentest Tools Nmap
- How To Hack
- Nsa Hacker Tools
- Hacker Tools
- Nsa Hack Tools Download
- Black Hat Hacker Tools
- Hack Tools 2019
- Hacking Tools For Windows 7
- Hacker Tools For Pc
- Tools 4 Hack
- Pentest Tools Download
- What Are Hacking Tools
- Hacking Tools Pc
- Hack Website Online Tool
- Pentest Tools Free
- Hacking Tools Pc
- Hacker Tools Linux
- Growth Hacker Tools
- Hacker Tools For Pc
- Pentest Tools For Mac
- Hacks And Tools
- New Hack Tools
- Hacking Tools For Windows
- Growth Hacker Tools
- Hacker Tools For Mac
- Android Hack Tools Github
- Hack Rom Tools
- Hacking App
- Pentest Tools Free
- Bluetooth Hacking Tools Kali
- Pentest Box Tools Download
- Hacking Tools Download
- Hacker Tools For Windows
- Pentest Tools List
- Pentest Tools For Mac
- What Is Hacking Tools
- Pentest Tools For Mac
- Pentest Tools Alternative
- Hacker Tools Apk Download
- Hacker Search Tools
- Top Pentest Tools
- Install Pentest Tools Ubuntu
- Hack Rom Tools
- Hacking Tools Free Download
- Hacker Tools
- Pentest Tools Open Source
- Hacker Tools Free Download
- Hack Tools For Windows
- Pentest Tools Download
- Best Hacking Tools 2019
- Hacker
- Hacker Tools Mac
- Hacking Tools Windows
- Pentest Tools Github
- Termux Hacking Tools 2019
- Hacking Tools For Games
- Hacking Tools For Windows 7
- Black Hat Hacker Tools
- Hacker Tools
- Pentest Tools Online
- Hacking Tools Windows 10









No comments:
Post a Comment